JUMP TO: THE CLIENT | THE CHALLENGE | THE APPROACH | ASSESSMENT FINDINGS | RESULTS | WHAT’S NEXT | NEXT STEPS
93% Critical Findings Closed | 78% High Findings Closed | 515 Weaknesses Remediated |
Key Results
- 515 weaknesses remediated across identity, Active Directory, legacy services, and patch management over five months.
- Critical findings dropped from 321 to 23 — a 93% reduction.
- High findings dropped from 214 to 48 — a 78% reduction.
- Sprint-based remediation model with a 10-person cross-functional working group meeting semi-weekly.
- Outcome: A repeatable patch management discipline with governance, prioritization, and cross-functional ownership — not just a one-time cleanup.
The Client
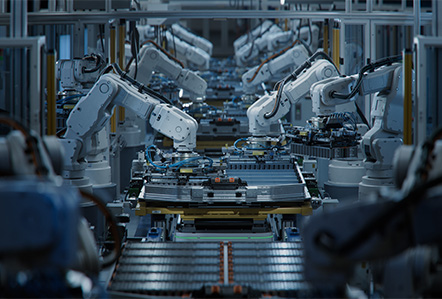
A large, globally distributed manufacturer with complex Windows infrastructure and a broad operational technology (OT) footprint. The company had accumulated significant security debt and internal teams lacked the bandwidth and tooling to systematically identify, prioritize and close vulnerabilities at scale.
Periodic patching efforts existed in name—but without formal policy, recurring governance or risk-based prioritization, the program had no real teeth.
The Challenge
An automated penetration testing assessment surfaced what the organization already suspected: the environment carried a dense concentration of exploitable weaknesses across identity, Active Directory, legacy services, and patch management.
Many of the findings mapped directly to attacker playbooks in active use — credential relay, NTLM coercion, credential dumping and lateral movement through misconfigured AD trust paths.
In other words, the risk was real, present and measurable.
The Approach
Inversion6 partnered with the client’s internal teams and a third-party technology partner to design and execute a structured, sprint-based remediation program.
Over five months, a core working group of ten people — spanning security, IT operations and leadership — met on a semi-weekly cadence to govern progress, resolve blockers and sustain momentum.
“One of the most important things we did, in addition to reducing risk, was share experiences about what worked — how to engage other teams, how to talk about priorities and how to develop repeatable processes. Building a patching program takes discipline, conviction and leadership. It’s an absolute grind.”
— Craig Burland, CISO, Inversion6
Three Principles Anchored the Engagement
- Risk-based prioritization — Critical and High findings drove the work queue using severity, exploitability and business exposure.
- Tooling as a forcing function — The team used automated penetration testing to validate real, exploitable risk and verify remediation.
- Leadership engagement — Decision-makers participated directly, eliminating delays and organizational friction.
Inversion6 provided the strategic framing, technical expertise and program leadership to keep the engagement focused and moving.
What the Assessment Revealed
| Risk Theme | Representative Findings | Business Risk |
|---|---|---|
| Identity & Authentication | Weak credentials, password spray exposure, local admin abuse | Unauthorized access, lateral movement |
| NTLM & AD Hardening | NTLM relay, SMB signing disabled, poisoning attacks | Domain-wide compromise |
| Legacy Services | Anonymous FTP, Telnet, insecure services | Expanded attack surface |
| Privilege Escalation | AD misconfigurations, credential dumping | Full enterprise takeover |
| Patch & Secrets | RCE vulnerabilities, exposed keys | Persistent attacker access |
Results
Over 5 sprints, the team closed 515 weaknesses — including 93% of Critical and 78% of High findings.
Critical findings dropped from 321 to just 23. High findings fell from 214 to 48.
Beyond the numbers, the organization gained something more important: a functioning patch management discipline with governance, prioritization and cross-functional ownership.
What’s Next
The tactical wins of this engagement are a foundation, not a finish line.
The remaining backlog and future findings will require sustained effort and a shift from project-based remediation to a long-term program.
- Formal patch management policies and SLAs
- Hardening standards across identity and infrastructure
- Dedicated resources and tooling
- Continuous vulnerability scanning
- Threat intelligence integration
Without these, environments inevitably backslide.
The goal is a program that continuously finds and closes vulnerabilities before attackers exploit them.