Some companies see cybersecurity as a cost center. We see things a little different. LEARN MORE >
-
Solutions
-
CISO Solutions
-
Managed Cybersecurity
-
Incident Response
-
-
About
-
About
-
-
-
Insights
-
-
Events
-
News
-
Our seasoned Chief Information Security Officers bring strategic guidance to your leadership team, helping you right-size your cybersecurity operations.
A full suite of manage solutions from our US-based Security Operations Center (SOC)—staffed 24x7x365 by a full team of experienced analysts.
You can count on our IR team to contain the damage from a cyberattack, investigate the origins of the breach and build better protections for the future.
Why Inversion6
With an abundance of solutions and providers, the task of choosing the right option is critical and can sometimes be overwhelming.
Contact UsCybersecurity Insights
Blog Posts

Blog
Claude Mythos & The Coming AI Vulnerability Storm
A new generation of AI is changing cybersecurity at an unprecedented pace. Claude Mythos demonstrates how quickly critical vulnerabilities can now be discovered and exploited—shrinking timelines from months to minutes. This blog breaks down what that means for organizations and outlines the key steps needed to stay ahead, from faster patching to AI-driven defenses and modernized incident response.

Blog
Threat Brief: Handala Hack Team
The report profiles the Handala Hack Team, a pro-Palestinian hacktivist group active since 2023 that conducts politically motivated cyberattacks, mainly targeting Israeli-related organizations and sectors like healthcare, defense, and technology. The group blends hacktivism with cyber-espionage and destructive operations, and may have ties to Iranian cyber activity.

Blog
Third-Party Risk Management: Why Vendor Security Is a Growing Threat
Third-party vendors are now responsible for many major cybersecurity breaches. Learn why third-party risk management (TPRM) is critical and how organizations can monitor vendor security risks.
Events

Event
i6 Google Event
Join Inversion6, TRG and Google to learn how the Android Enterprise Trust Partner ecosystem uses device signals to control access across managed and unmanaged endpoints.

Event
CISO de Mayo Event
Each year, Inversion6 celebrates Cinco de Mayo with our own unique twist at our annual CISO de Mayo event, bringing together local cybersecurity leaders and IT professionals for great food, drinks and conversation
Case Studies

Case Study
Turning Threat Intelligence into Proactive Security
A global manufacturer needed more than awareness—they needed actionable intelligence. This case study shows how weekly threat briefings transformed their security posture, improved compliance and enabled proactive risk mitigation.
Case Study
Turning Security Debt into a Solid Foundation with Patch Management
A global manufacturer faced hundreds of exploitable vulnerabilities and no structured way to fix them. This case study shows how a sprint-based patch management program helped eliminate critical risk, remediate over 500 weaknesses and establish a long-term security foundation.

Case Study
When Compliance Becomes Your Competitive Advantage
A fast-growing startup hit a wall when enterprise clients started asking for SOC 2 Type II. Without a formal security program, deals were at risk. This case study shows how a fractional CISO helped them build a compliant, audit-ready security posture—turning a blocker into a growth driver and ultimately supporting a successful acquisition.
Webinars
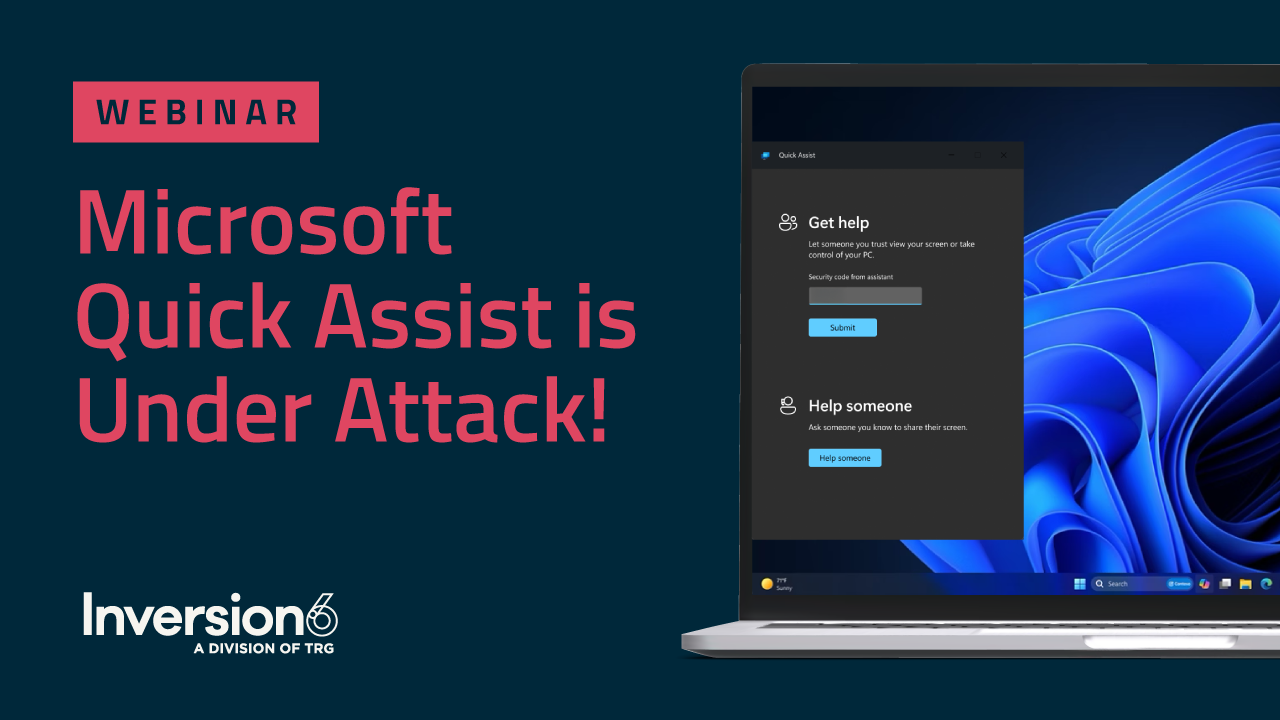
Webinar
Microsoft Quick Assist is Under Attack: What You Need to Know
It’s time to talk about Microsoft Quick Assist. It may be a great tool for streamlining IT support, but it’s also becoming a popular target for hackers trying to break into your systems.

Webinar
Simplifying Cybersecurity Compliance in Food Service
Discover how to navigate cybersecurity compliance challenges in the food service industry. Join Inversion6’s free webinar for actionable tips, industry insights, and real-world strategies to keep your business protected and compliant.

Webinar
How to Go All-in on Cybersecurity
You see cyber threats are becoming more sophisticated. You’re worried about compliance measures enhancing. You’re hunting for cybersecurity personnel, who are growing difficult to find.
eBooks

eBook
How To Fail at Cybersecurity
A more resilient profile needs strong cybersecurity principles. Learn what that entails with ‘How to Fail at Cybersecurity’ from Inversion6.

eBook
You're Headed to the Cloud. The Question is: Are You Ready?
Cloud migration has given businesses like yours the opportunity to outmaneuver constraints and reinvent what they do and offer.

eBook
Combat the FBI's #1 Cyber Threat: Business Email Compromise
BEC remains a top cybersecurity concern and is one of the most financially damaging online crimes executed.
Talk with one of our experts
Schedule a free consultation to learn how Inversion6 cybersecurity services can enhance your existing program and keep your organization safe from cyberattacks and security threats.

