Blog

Blog Post V 2
Turning Threat Intelligence into Proactive Security
A global manufacturer needed more than awareness—they needed actionable intelligence. This case study shows how weekly threat briefings transformed their security posture, improved compliance and enabled proactive risk mitigation.
Blog Post V 2
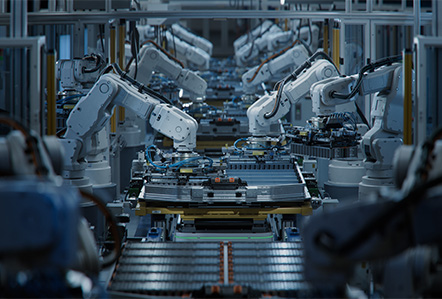
Turning Security Debt into a Solid Foundation with Patch Management
A global manufacturer faced hundreds of exploitable vulnerabilities and no structured way to fix them. This case study shows how a sprint-based patch management program helped eliminate critical risk, remediate over 500 weaknesses and establish a long-term security foundation.

Blog Post V 2
Claude Mythos & The Coming AI Vulnerability Storm
A new generation of AI is changing cybersecurity at an unprecedented pace. Claude Mythos demonstrates how quickly critical vulnerabilities can now be discovered and exploited—shrinking timelines from months to minutes. This blog breaks down what that means for organizations and outlines the key steps needed to stay ahead, from faster patching to AI-driven defenses and modernized incident response.

Blog Post V 2
When Compliance Becomes Your Competitive Advantage
A fast-growing startup hit a wall when enterprise clients started asking for SOC 2 Type II. Without a formal security program, deals were at risk. This case study shows how a fractional CISO helped them build a compliant, audit-ready security posture—turning a blocker into a growth driver and ultimately supporting a successful acquisition.

Blog Post V 2
Threat Brief: Handala Hack Team
The report profiles the Handala Hack Team, a pro-Palestinian hacktivist group active since 2023 that conducts politically motivated cyberattacks, mainly targeting Israeli-related organizations and sectors like healthcare, defense, and technology. The group blends hacktivism with cyber-espionage and destructive operations, and may have ties to Iranian cyber activity.

Blog Post V 2
Third-Party Risk Management: Why Vendor Security Is a Growing Threat
Third-party vendors are now responsible for many major cybersecurity breaches. Learn why third-party risk management (TPRM) is critical and how organizations can monitor vendor security risks.

